Spend Less Time Responding to Security Questionnaires
Security Assessments, Security Questionnaires, Vendor Assessments, Vendor Security Questionnaires, Technical RFPs–whatever you call them–are unavoidable in the world of Software-as-a-Service (SaaS) and are a pain to complete. Moreover, they’re a big part of closing new opportunities and maintaining or up-selling existing accounts.
But what many people don’t realize is that the Security Assessment response process can be made less painful and, dare we say, fun.
To make your security questionnaire process a little bit faster, we’re going to share some common questions that tend to appear so you can get a leg up on building your content and responding to security questionnaires.
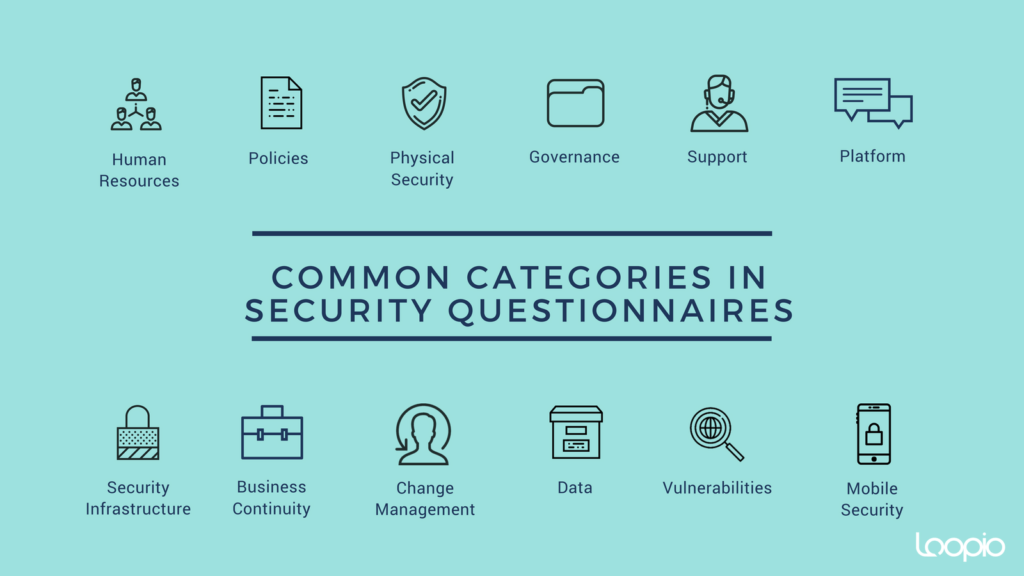
Common Questions in Vendor Security Questionnaires:
Human Resources
- Are employees subject to background checks? Please describe the type and level of background check.
- Are employees required to sign NDA or confidentiality agreements?
- Describe any employee access to client data.
Policies
- Is there a security incident management process in place? Please describe.
- How frequently are your information security policies reviewed?
- Is there a formal process for reporting and responding to privacy complaints or privacy incidents? Please describe.
Physical Security
- Are visitors permitted? Please describe what locations within your office(s) visitors have access to.
- Please describe security systems in place for visitors, including badges, supervision, and sign-in systems.
- Are closed-circuit cameras utilized at all entrances and exits in your offices?
Security Infrastructure
- What third-party audits are regularly performed?
- What third-party security certifications does your organization have? When were these last updated?
- Does your organization run intrusion detection or intrusion protection on the network?
Business Continuity
- Do you have alternate data centres in case of disasters?
- Does your solution support redundancy and load balancing?
- What is the recovery time from failure due to technical issues?
Our goal is to make your life simpler. Here’s a handy template to access these commonly asked questions from vendor security questionnaires and more–download it to get your Library started.
The answers to these questions will form the base of your security content library when responding to security questionnaires. Having a searchable Library through RFI software, bid management software, security questionnaire automation, or DDQ tools will help make this content reusable so you and your team can leverage it for that next Security Questionnaire that comes in through the door.


